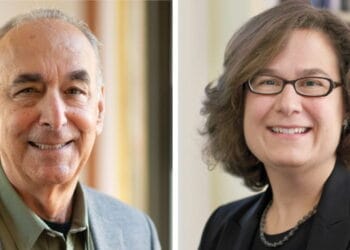
Cybersecurity incidents pose a elementary problem: How do you reassure stakeholders whereas acknowledging that many details stay unknown early in forensic investigations? Jena Valdetero and Wouter van Wengen of Greenberg Traurig and Jonah Pitkowsky, Lily Williams and Jamie Singer of FTI Consulting study how risk actors more and more make use of triple extortion techniques, from encrypting and exfiltrating information to DDoS assaults and swatting that brings cyber threats to executives’ literal entrance doorways, requiring cautious coordination between authorized counsel and communications professionals to construct messaging that adapts to evolving eventualities.
In a great world, every part goes in accordance with plan. You snag the tickets to the sold-out present, it stops raining earlier than you permit for work, and your prepare is operating proper on time. We love these moments as a result of no one likes a curveball. However issues don’t all the time go in accordance with plan, and in these moments the place a response is required, what we are saying issues.
When responding to a cyber incident, the stakes related to offering the precise info on the proper time are excessive, particularly when risk actors escalate conditions and details change rapidly. The flexibility to deploy the precise technique, whether or not fast stakeholder communication, authorized steering or technical containment, can decide whether or not a corporation preserves or loses belief.
Cybersecurity incidents pose a elementary problem: How do you reassure stakeholders and retain their confidence all through an incident whereas acknowledging that, particularly early on in a forensic investigation, many details are nonetheless unknown? It takes time to analyze the complete scope of an incident and to validate the actions of risk actors. Coupled with more and more aggressive risk actor techniques, notably in a cyber extortion occasion, these realities make sharing details about an incident perilous since details can usually change.
In a world the place cyberattacks are growing in frequency, stakeholders from prospects to staff to regulators scrutinize how effectively a sufferer group handles its response. Navigating this problem requires a holistic strategy knowledgeable by the most recent risk intelligence and cautious coordination among the many sufferer group, exterior authorized counsel and cyber communications professionals.
Speaking by means of double and triple extortion incidents
Practically all ransomware incidents nowadays contain various ranges of extortion. Not solely do risk actors usually encrypt techniques or information to render them inaccessible to the sufferer group, however risk actors regularly additionally steal massive portions of information and threaten to put up the information on-line except a ransom is paid. Risk actors typically make use of extra strain techniques, like harassment of staff or continued assaults on the sufferer’s techniques, to coerce a sufferer into paying a ransom.
Step one to speaking with confidence by means of a double or triple extortion incident is to be taught the details and plan for potential escalations. If the risk actor is understood, a sufferer group can put together for potential escalations with data of that actor’s strategies and patterns of conduct. For instance, the Akira ransomware group was, for plenty of years, a pure extortion operation: It exfiltrated and held information ransom however didn’t encrypt techniques within the course of. In 2024, specialists realized the group had once more begun to encrypt techniques, inflicting extra issues for response and restoration.
When delicate information is concerned, a sufferer group might have obligations below information privateness and safety legal guidelines to inform affected people and/or regulators and should have contractual obligations to inform different third events of an incident affecting their information. Cautious communications are key to making sure stakeholders obtain the precise info on the proper time.
Throughout a triple extortion occasion, the place information is encrypted, exfiltrated and the risk actor locations extra strain on the sufferer group, whether or not by means of a distributed denial-of-service (DDoS) assault or aggressive outreach to stakeholders, communications groups should be ready for a number of waves of messaging that acknowledge the evolving nature of threats. An organization can not anticipate each attainable escalation tactic, however they will mitigate threat by constructing messaging that’s adaptable to quite a lot of eventualities.
By way of considerate state of affairs planning and shut coordination between authorized and communications specialists, organizations can put together for these extortion curveballs in step with contractual, regulatory and litigation issues, all whereas preserving attorney-client privilege over the drafting of communications.
Swatting and different stressors
Some risk actor curveballs intend to hit nearer to dwelling and require an particularly cautious strategy. One such escalation is “swatting,” an aggressive tactic the place the risk actor makes a hoax name to legislation enforcement claiming an emergency is underway to attract a big response to the house of a sufferer group’s executives or to the enterprise itself. Even the specter of swatting may cause main public concern, reminiscent of a latest instance of a cybercriminal threatening to make use of swatting towards sufferers at a hospital that had not paid a ransom.
Bringing a cyber incident to a sufferer’s literal entrance door blurs the strains between cyber threats and bodily safety and weaponizes worry to encourage fee. The primary occasion of swatting is usually a shock and may make a sufferer group look unprepared. Organizations dealing with swatting threat should be ready to speak rapidly to keep away from missteps and prioritize the security of inside stakeholders.
This messaging must be drafted in shut coordination with authorized, legislation enforcement and risk intel specialists, to supply directions on how doubtlessly at-risk people can shield themselves. Although swatting makes an attempt may be unpredictable and personally difficult, assuring stakeholders the difficulty is being dealt with can go a protracted solution to retaining belief when it issues most.
Ransomware hoaxes and risk actor lies
Difficult questions come up when the state of affairs adjustments unexpectedly, reminiscent of how do you reassure key stakeholders when ransom notes are despatched to staff … though there’s no proof an assault ever occurred?
In latest months, impersonators of risk actor group BianLian circulated ransom notes to enterprise executives, demanding fee in bitcoin. This run-of-the-mill ransomware escalation tactic has one key distinction: On this case, there was no proof an assault had even occurred. Executives had been confronted with a problem: Whereas it could be tempting to disclaim the legitimacy of the notes, making definitive statements it’s possible you’ll have to stroll again later erodes belief excess of taking time to collect the details. So how ought to a corporation reply?
What not to do: refute the claims in public straight away. Making definitive statements opens up a corporation to potential popularity threat and authorized legal responsibility if new proof emerges and there’s authentic risk actor exercise. On this state of affairs, the corporate ought to reassure stakeholders the group is investigating claims and responding to the state of affairs as they collect the details.
Cybersecurity incidents pose a elementary problem: How do you reassure stakeholders whereas acknowledging that many details stay unknown early in forensic investigations? Jena Valdetero and Wouter van Wengen of Greenberg Traurig and Jonah Pitkowsky, Lily Williams and Jamie Singer of FTI Consulting study how risk actors more and more make use of triple extortion techniques, from encrypting and exfiltrating information to DDoS assaults and swatting that brings cyber threats to executives’ literal entrance doorways, requiring cautious coordination between authorized counsel and communications professionals to construct messaging that adapts to evolving eventualities.
In a great world, every part goes in accordance with plan. You snag the tickets to the sold-out present, it stops raining earlier than you permit for work, and your prepare is operating proper on time. We love these moments as a result of no one likes a curveball. However issues don’t all the time go in accordance with plan, and in these moments the place a response is required, what we are saying issues.
When responding to a cyber incident, the stakes related to offering the precise info on the proper time are excessive, particularly when risk actors escalate conditions and details change rapidly. The flexibility to deploy the precise technique, whether or not fast stakeholder communication, authorized steering or technical containment, can decide whether or not a corporation preserves or loses belief.
Cybersecurity incidents pose a elementary problem: How do you reassure stakeholders and retain their confidence all through an incident whereas acknowledging that, particularly early on in a forensic investigation, many details are nonetheless unknown? It takes time to analyze the complete scope of an incident and to validate the actions of risk actors. Coupled with more and more aggressive risk actor techniques, notably in a cyber extortion occasion, these realities make sharing details about an incident perilous since details can usually change.
In a world the place cyberattacks are growing in frequency, stakeholders from prospects to staff to regulators scrutinize how effectively a sufferer group handles its response. Navigating this problem requires a holistic strategy knowledgeable by the most recent risk intelligence and cautious coordination among the many sufferer group, exterior authorized counsel and cyber communications professionals.
Speaking by means of double and triple extortion incidents
Practically all ransomware incidents nowadays contain various ranges of extortion. Not solely do risk actors usually encrypt techniques or information to render them inaccessible to the sufferer group, however risk actors regularly additionally steal massive portions of information and threaten to put up the information on-line except a ransom is paid. Risk actors typically make use of extra strain techniques, like harassment of staff or continued assaults on the sufferer’s techniques, to coerce a sufferer into paying a ransom.
Step one to speaking with confidence by means of a double or triple extortion incident is to be taught the details and plan for potential escalations. If the risk actor is understood, a sufferer group can put together for potential escalations with data of that actor’s strategies and patterns of conduct. For instance, the Akira ransomware group was, for plenty of years, a pure extortion operation: It exfiltrated and held information ransom however didn’t encrypt techniques within the course of. In 2024, specialists realized the group had once more begun to encrypt techniques, inflicting extra issues for response and restoration.
When delicate information is concerned, a sufferer group might have obligations below information privateness and safety legal guidelines to inform affected people and/or regulators and should have contractual obligations to inform different third events of an incident affecting their information. Cautious communications are key to making sure stakeholders obtain the precise info on the proper time.
Throughout a triple extortion occasion, the place information is encrypted, exfiltrated and the risk actor locations extra strain on the sufferer group, whether or not by means of a distributed denial-of-service (DDoS) assault or aggressive outreach to stakeholders, communications groups should be ready for a number of waves of messaging that acknowledge the evolving nature of threats. An organization can not anticipate each attainable escalation tactic, however they will mitigate threat by constructing messaging that’s adaptable to quite a lot of eventualities.
By way of considerate state of affairs planning and shut coordination between authorized and communications specialists, organizations can put together for these extortion curveballs in step with contractual, regulatory and litigation issues, all whereas preserving attorney-client privilege over the drafting of communications.
Swatting and different stressors
Some risk actor curveballs intend to hit nearer to dwelling and require an particularly cautious strategy. One such escalation is “swatting,” an aggressive tactic the place the risk actor makes a hoax name to legislation enforcement claiming an emergency is underway to attract a big response to the house of a sufferer group’s executives or to the enterprise itself. Even the specter of swatting may cause main public concern, reminiscent of a latest instance of a cybercriminal threatening to make use of swatting towards sufferers at a hospital that had not paid a ransom.
Bringing a cyber incident to a sufferer’s literal entrance door blurs the strains between cyber threats and bodily safety and weaponizes worry to encourage fee. The primary occasion of swatting is usually a shock and may make a sufferer group look unprepared. Organizations dealing with swatting threat should be ready to speak rapidly to keep away from missteps and prioritize the security of inside stakeholders.
This messaging must be drafted in shut coordination with authorized, legislation enforcement and risk intel specialists, to supply directions on how doubtlessly at-risk people can shield themselves. Although swatting makes an attempt may be unpredictable and personally difficult, assuring stakeholders the difficulty is being dealt with can go a protracted solution to retaining belief when it issues most.
Ransomware hoaxes and risk actor lies
Difficult questions come up when the state of affairs adjustments unexpectedly, reminiscent of how do you reassure key stakeholders when ransom notes are despatched to staff … though there’s no proof an assault ever occurred?
In latest months, impersonators of risk actor group BianLian circulated ransom notes to enterprise executives, demanding fee in bitcoin. This run-of-the-mill ransomware escalation tactic has one key distinction: On this case, there was no proof an assault had even occurred. Executives had been confronted with a problem: Whereas it could be tempting to disclaim the legitimacy of the notes, making definitive statements it’s possible you’ll have to stroll again later erodes belief excess of taking time to collect the details. So how ought to a corporation reply?
What not to do: refute the claims in public straight away. Making definitive statements opens up a corporation to potential popularity threat and authorized legal responsibility if new proof emerges and there’s authentic risk actor exercise. On this state of affairs, the corporate ought to reassure stakeholders the group is investigating claims and responding to the state of affairs as they collect the details.